- Ransomware is malware that locks or encrypts systems and data to extort the victim through payment, usually in cryptocurrencies.
- It has evolved from simple blockers to complex double and triple extortion models, supported by Ransomware-as-a-Service.
- Prevention involves updating systems, using good security, training users, and maintaining isolated backups.
- Paying the ransom never guarantees recovery and fuels the criminal business, so it is recommended to restore backups and use specialized tools and authorities.
El Ransomware has become one of the most profitable and dangerous cyberattacks. of recent years. It locks computers, encrypts files, and demands payment, usually in cryptocurrency, in exchange for restoring access. It affects individual users as well as businesses, hospitals, city councils, and even critical infrastructure.
Far from being something new, The history of ransomware begins in the late 80s and has become increasingly sophisticated. Over time: it was first distributed on floppy disks and asked for money by mail; today it spreads in seconds through entire networks, uses advanced cryptography and relies on business models such as Ransomware-as-a-Service that allow any criminal to launch campaigns with hardly any technical knowledge.
What is ransomware and how does it work?
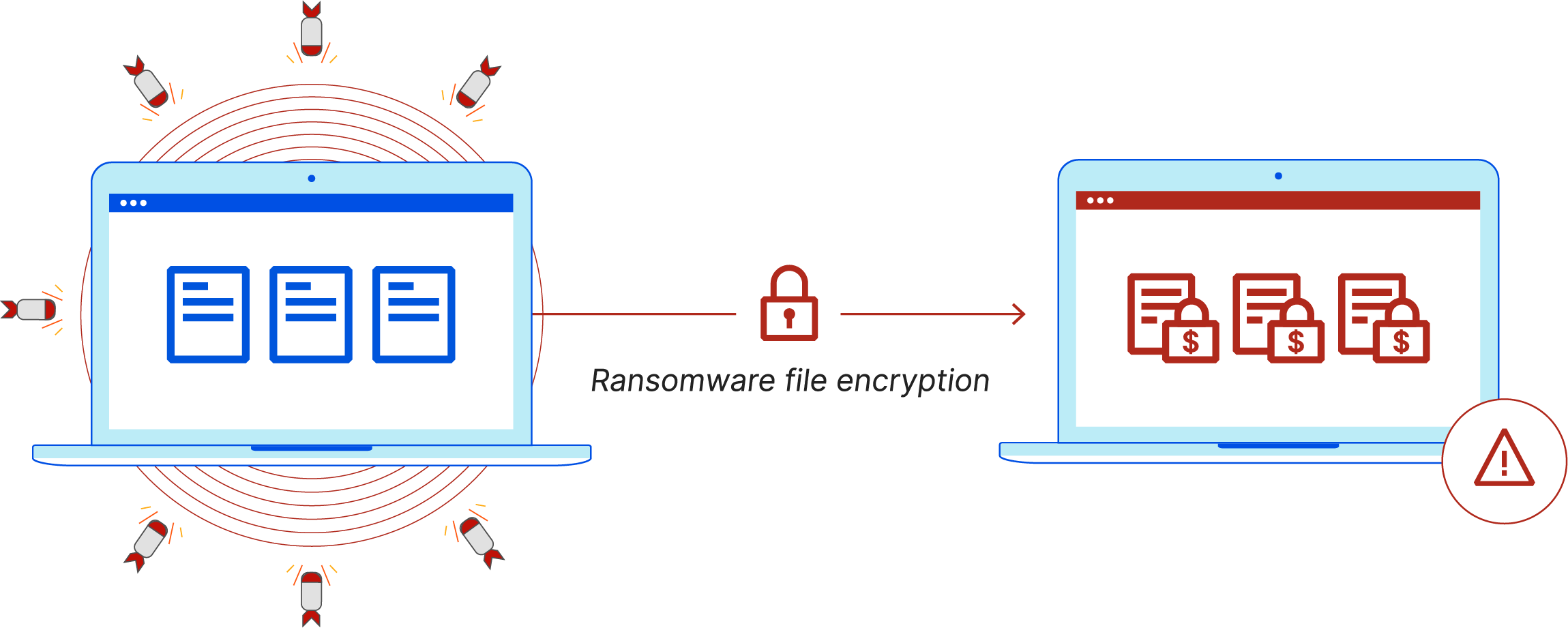
In simple terms, Ransomware is a type of malware designed to prevent you from using your computer or accessing your data. Unless you pay a ransom. It can block access to the entire system, encrypt documents, databases, photos, or even the entire disk, and display a message with payment instructions.
In a typical attack, The cybercriminal compromises a device or network, deploys malware, and holds the information hostage.From there, the extortion begins: they threaten not to return the decryption key, to publish the stolen data, or directly to destroy it if payment is not made within a certain period.
It is important to be clear that Paying the ransom guarantees absolutely nothing.Many victims do not recover their files even after paying; others receive faulty tools that further corrupt the data. Furthermore, payment fuels the criminal enterprise and can make the victim a repeat target.
Therefore, in case of infection, the recommendations of experts and organizations such as INCIBE or the FBI itself They are clear: do not pay, isolate the affected systems, restore backups and report the incident to the competent authorities.
Historical evolution of ransomware
The timeline of ransomware shows how it has gone from a technical curiosity to a multi-billion dollar criminal industry. Each milestone has introduced improvements in encryption, propagation, or extortion techniques..
1989 – AIDS Trojan or “PC Cyborg”This is considered the first documented case of ransomware. It was distributed on floppy disks related to AIDS information. The malware hid system file directories and demanded $189 to unlock them, with payment to be made by mail to an address in Panama. Technically, it was rudimentary. It did not encrypt the content of the files, only their names.which allowed the damage to be reversed without paying.
1996 – The concept of “cryptoviral extortion” is bornResearchers Adam L. Young and Moti Yung described at the IEEE Security and Privacy conference how malware could use asymmetric cryptography to extort its victims. The malicious code included a public key, encrypted files, and forced the victim to send encrypted text to the attacker to recover the private key. in exchange for money. That was still academic theory, but it exactly foreshadowed what we would see later.
Early 2000s – First modern outbreaksAfter a period of isolated incidents, In 2005 a notable increase in infections beganespecially in Russia and Eastern Europe. The first variants that seriously employed asymmetric cryptography appeared, which greatly complicated decryption without the attacker's key.
2009 – Cryptocurrencies arriveThe creation of Bitcoin marked a turning point. Payments shifted from checks, transfers, or prepaid cards to hard-to-trace virtual currenciesThis relative anonymity made the model much more attractive and scalable for organized crime.
2013 – Modern Ransomware Era: CryptoLockerCryptoLocker popularizes strong encryption on a large scale: 2048-bit RSA keys, files encrypted by extension, and ransoms demanded in Bitcoin or prepaid vouchersIts impact was such that it required international operations to take down the infrastructure (Gameover Zeus) that supported it.
2015 – Ransomware-as-a-Service (RaaS)Variants like Tox introduce the RaaS model: ransomware creators offering ready-to-use “kits” to other criminalsIn exchange for a commission on the ransoms. This democratizes attacks: you no longer need to know how to program to launch a campaign.
2016-2017 – Global wave and crypto wormsIn 2016, ransomware families like Mamba emerged, which encrypts the entire disk at the boot level using tools like DiskCryptor. In 2017, WannaCry (WanaCrypt0r) appeared. the first massively replicating cryptoworm, which exploits the MS17-010 vulnerability in Windows and encrypts data from more than 75.000 computers worldwide, including British hospitals, Spanish companies such as Telefónica, and Russian infrastructure.
Also in 2017 Petya and its variants attack by encrypting the master file table (MFT)disabling the system, and large-scale campaigns against banks, energy companies, and public administrations are documented. The use of messages that impersonate police forces to lend "legitimacy" to extortion is becoming widespread.
2018 – Ryuk and the “big game hunt”. Ryuk focuses on high-value objectives: public bodies, hospitals, media outlets and large companiesIt uses unique keys per organization and advanced propagation capabilities (Wake on LAN, SMB, RPC), which complicates both response and decryption.
2019 – Double and triple extortionSince this year, ransomware groups have adopted the tactic of double extortion: They not only encrypt the data, they also exfiltrate it and threaten to publish it. If payment isn't made. There are even triple extortion schemes, where the victim's clients, suppliers, or patients are also pressured. Incident response teams like IBM Security X-Force confirm that almost all the cases they handle now involve data theft.
2020 – Boom during COVID-19Mass teleworking, the rush to enable remote access, and the reduced security of many homes are driving up attacks. Governments, financial institutions, and especially the healthcare sector are experiencing a significant increase of ransomware incidents during the pandemic.
2022 – Email thread hijackingA particularly deceptive technique is gaining prominence: “thread hijacking”. The criminals infiltrate legitimate email conversations and respond within the same thread. with malicious attachments or links, greatly increasing the click rate.
2023-2024 – Beyond encryptionAs defenses and backups improve, many gangs are expanding their arsenal: They combine ransomware with data thieves (stealers) They extract credentials and sensitive data without needing to lock down systems. Groups like LockBit or remnants of Conti resort to outright data theft and blackmail, even when they don't activate encryption.
Main types of ransomware
Although there are countless variations, Most current ransomware can be grouped into two large familiesThe first is the one that encrypts information and the one that blocks the device. From there, additional subtypes and extortion strategies emerge.
Encrypting ransomware
He is the most feared and the one who usually makes the headlines. Its goal is to encrypt critical files or data so that they can only be recovered with a key held by the attacker.It usually focuses on office documents, databases, accessible backups, production systems, etc.
In theory, after paying the ransom, the criminal sends a decryption key or tool which reverses the process. In practice, there are many cases where the victim receives nothing useful, or where the decryption fails and some of the information is damaged forever.
Locker ransomware
In this case, the malware It prevents access to the entire device by displaying a full-size screen. It takes up the entire desktop and prevents you from using the system. It's more common on mobile phones and some home computers.
Unlike pure encryption, The files aren't always accessed here.When the infection is removed or the system is restored, the data may remain intact. The ransom note often includes logos of law enforcement agencies or warnings of alleged illegal activities.
Other common subtypes
Based on these two foundations, several variations and labels emerge that are useful to know in order to better identify the risk:
- Scareware or intimidation softwareIt presents itself as an antivirus or security tool that "detects" fake infections and demands payment to clean them. It bombards you with pop-ups, but often It doesn't encrypt or block anything, it just tricks the user.
- Classic screen locksThey display a static screen, often with logos of police or government agencies, indicating that illegal content (piracy, pornography, etc.) has been detected and that a "fine" must be paid. Their goal is to scare, not so much technical sophistication..
- doxwareThe attacker steals private information (photos, documents, histories, databases) and threatens to publish it. The pressure is not based on losing access to the data, but on shame, reputational damage, or possible sanctions by filtration.
- Double and triple extortion ransomwareIt combines encryption + data theft and, in some cases, Additional attacks such as DDoS or blackmail of involved third parties (clients, patients, partners) to maximize pressure.
- destructive ransomwareInstead of focusing on the actual rescue, He threatens to delete or overwrite the information if payment is not made.And sometimes it does so even after receiving the money. It's closer to sabotage than classic extortion.
How ransomware spreads
For an attack to be successful, the criminal needs a point of entry. Ransomware often arrives as a "passenger" inside emails, downloads, or unpatched vulnerabilities..
Malspam (malicious spam)It's the mass-firing tactic. The attacker sends thousands or millions of emails with trap attachments (PDF, Word, ZIP) or links to compromised sites. Simply opening the file or enabling macros is enough for the malware to download and execute.
Malvertising (malicious advertising)It takes advantage of banners on legitimate or compromised websites. Simply accessing the page can silently redirect the user to a server controlled by the attacker.There, an exploit kit analyzes the browser, plugins, and system, and launches the attack by taking advantage of any available vulnerabilities, often without the user clicking on anything.
Spear phishing and whalingUnlike mass spam, Spear phishing targets very specific objectives.A company, a department, an executive. The emails are meticulously crafted, based on real data (for example, LinkedIn organizational charts), and impersonate individuals such as the CEO or HR manager. "Whaling" targets high-level positions, where a single click can open the door to the entire corporate network.
Social engineering in generalThe attackers obtain information from social media, corporate websites, or previous leaks, and They use it to make the message seem legitimate and familiar.Sometimes they impersonate technical support, the bank, the software provider, or even a co-worker, reducing the user's suspicions.
Furthermore, Many modern attacks exploit software vulnerabilitiesexposed services (such as poorly secured RDP), weak passwords, or pirated softwareOnce inside the network, the ransomware combines with other tools to move laterally, steal credentials, and locate the most valuable systems before triggering the encryption.
Ransomware on computers, Macs and mobile phones
Although most media incidents involve Windows, no platform is completely safe.
En WindowsThe attack surface is larger due to its market share and the amount of third-party software installed. Families such as CryptoLocker, CryptoWall, Petya, WannaCry, Ryuk, TeslaCrypt, and Mamba have had a massive impact, encrypting files, entire disks, and automatically propagating across networks; see Shadow Copy tutorial.
En MacThe first high-profile case was KeRanger in 2016, which slipped in as a compromised version of a legitimate app (Transmission). It would copy in the background, wait a few days, and then start encrypting files.Later, others appeared, such as Findzip or MacRansom, and also fake ransomware such as ThiefQuest/EvilQuest that actually functioned as "wipers", destroying data without any real intention of decryption.
En Android phonesAbove all, screen blockers have proliferated that They display messages alleging illegal activities and demand payment to unlock the device.They usually hide in apps downloaded from outside official stores or in apps of dubious origin. In many cases, they can be removed by booting into safe mode and uninstalling the malicious app, but some variants require a complete reset.
Notable ransomware cases and families
Over the years, the following have been identified dozens of families with varied tactics and objectives. Some of the best known are:
- RevetonHe popularized screen locks with logos of supposed law enforcement agencies. He displayed the IP address, internet provider, and even a webcam image to intimidate the victim and demand payment through prepaid cards or anonymous services.
- CryptoLockerOne of the great pioneers of strong mass encryption. It generated RSA key pairs, encrypted files by extension, and demanded Bitcoin.Its infrastructure was neutralized when the Gameover Zeus botnet was dismantled.
- CryptoWall. Subsequent evolution, distributed through phishing campaigns and exploit kits. It reached versions such as CryptoWall 3.0 and was associated with groups, supposedly of Russian origin.
- TeslaCryptInitially focused on the world of video games (encrypting games and related content), he eventually retired when The master decryption key was leakedThis allowed security companies to create free tools to recover the files.
- MambaInstead of encrypting individual files, Encrypt the entire disk at the boot level using DiskCryptorIt creates specific users, modifies the MBR, and prevents the system from booting without the key.
- WannaCryThe paradigmatic case of a cryptographic worm. It exploited a Windows vulnerability (EternalBlue/MS17-010) and spread automaticallyaffecting hospitals, energy companies, transport and thousands of organizations worldwide until a “kill switch” was accidentally activated.
- RyukFocused on large organizations, It uses custom keys per victim, worm capabilities, and additional tools to navigate the network. It has been seen in attacks on public administrations, media outlets, and essential services.
Ransomware-as-a-Service (RaaS): the business behind the crime
One of the reasons for the rise of ransomware is its business model. Ransomware-as-a-Service operates like a criminal franchise where everyone has their role.
The developers create the malware and a web infrastructure where “affiliates” can Configure campaigns, customize ransom notes, set amounts, and monitor statistics (infected victims, payments received, etc.). In return, the creator keeps a percentage of each ransom.
There have been and are multiple “brands” of RaaS: Cerber, Stampado, Philadelphia, Frozr Locker, Satan, RaasBerry, Atom, Hostman, Shark, GrandCrab, Ako, LockBit and many more. Some are even advertised in underground forums with brochures, videos, and "technical support" for less experienced criminals.
With this model, The risk is spread and the barrier to entry is very lowSimply pay a fee or share profits to launch attacks that would otherwise require advanced knowledge of programming, cryptography, and networks.
What to do if you get infected with ransomware
When the ransom note pops up, The instinctive reaction is usually panic.But it's important to act sensibly to limit the damage.
The first is Disconnect the device from the network (cable, Wi-Fi, etc.) and turn off other connected devices that may be at risk, especially if you share files or network drives. This helps to slow the spread.
Next, and whenever possible, Consult your IT team, a cybersecurity specialist, or public help services. (In Spain, INCIBE's 017 helpline offers free and confidential support.) They will be able to analyze the variant, assess options, and guide you on the next steps.
If you have reliable backups, The safest solution is usually to format the affected computers and restore backupsAny attempt to "clean" without a clean install may leave traces of malware and allow reinfections.
In the absence of backups, There are initiatives like No More Ransom what are you offering free decryption tools for certain known families. They don't cover all variants or all versions, but in some cases they allow you to recover files for free.
In any scenario, You must report the incident to the authoritiesBeyond any support you may receive, your data will help improve threat intelligence and prosecute those responsible.
How to prevent ransomware attacks
The best strategy against ransomware is clear: Invest in prevention and accept that sooner or later there will be attempted attacks.The idea is to minimize the chances of success and the impact should it occur.
From a technical standpoint, it is advisable Keep operating systems, applications, and firmware updated and patched by patch managementMany campaigns exploit vulnerabilities for which patches have been available for some time. Enabling automatic updates, when possible, greatly reduces the window of exposure.
It is also essential have reliable security solutions (antimalware, antiransomware, antiexploit, antispam filters) on personal computers, servers, and mobile devices. A good product can detect typical mass encryption behavior and stop the process before it affects the entire system. See comparisons of reliable security solutions For businesses.
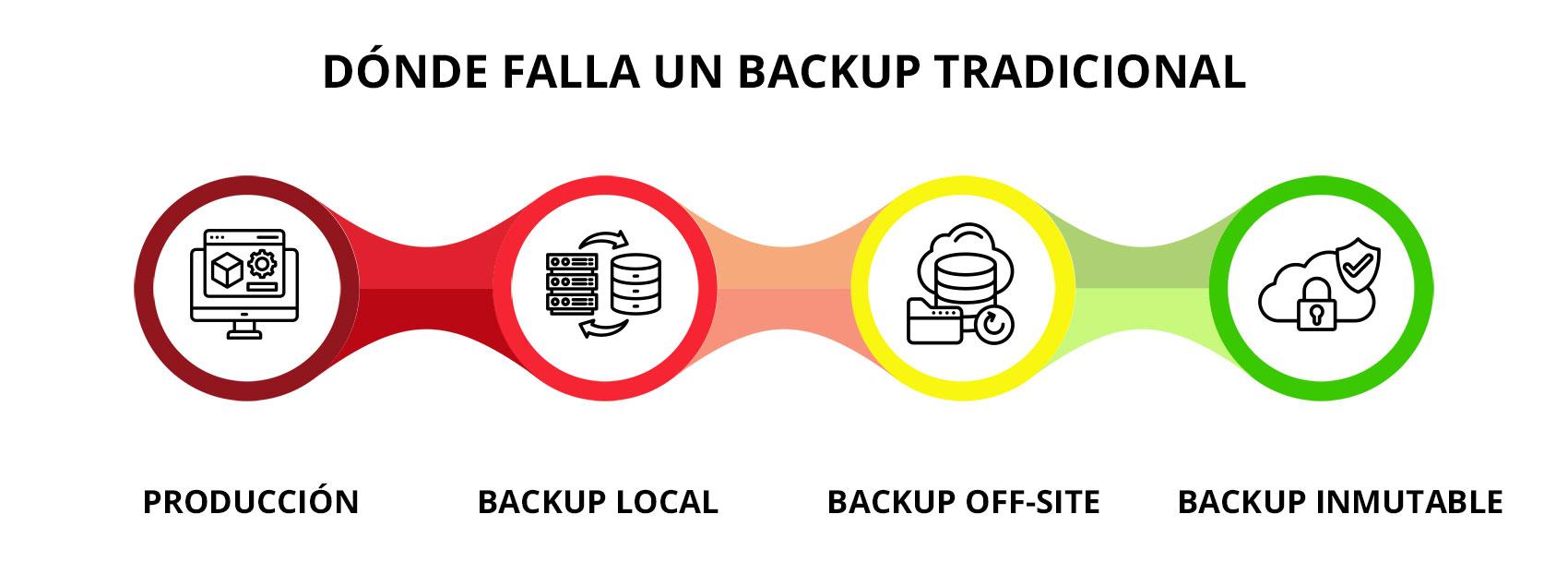
Another critical measure is Implement a robust backup policyIdeally, you should combine cloud backups (with encryption and multi-factor authentication) with offline copies on external drives or NAS serversTapes or other storage media should be physically disconnected when not in use. This prevents ransomware from encrypting backups as well.
In the organizational sphere, User training and awareness are keyClearly explaining what phishing is, how to recognize suspicious emails, why you shouldn't enable macros unnecessarily, or download unexpected attachments makes a big difference. Tools like phishing simulations help reinforce these best practices. Learn more about training and awareness.
Some basic guidelines that greatly reduce the risk are:
- Do not open attachments from unknown or unexpected senders., even if they appear to come from trusted contacts, without first verifying through another channel.
- Hover your mouse over the links to see the actual URL And if you're unsure, type the address manually into your browser instead of clicking.
- Avoid browsing or downloading software from websites of dubious originespecially when they offer "free" programs that are normally paid for.
- Reduce the use of pirated software, as it often comes with embedded malicious code.
In companies, moreover, It is recommended to apply the principle of least privilege, segment networks, and protect exposed services (such as RDP) with VPN and multifactor authentication.and have an incident response plan in place that includes what to do specifically in the event of a ransomware attack.
The volume of attacks, the multimillion-dollar payouts, and the creativity of the gangs make it clear that Ransomware will continue to be a recurring threat for years to come.Keeping systems up to date, making backups, using serious security solutions and, above all, cultivating a good cyber hygiene culture at home and in the company are the pillars that make the difference between a controlled scare and a major disaster that completely paralyzes activity.
Passionate writer about the world of bytes and technology in general. I love sharing my knowledge through writing, and that's what I'll do on this blog, show you all the most interesting things about gadgets, software, hardware, tech trends, and more. My goal is to help you navigate the digital world in a simple and entertaining way.