- Kernel isolation and memory integrity use VBS to protect the kernel and critical processes from advanced attacks.
- Enabling it significantly improves security, although it may impact the performance and compatibility of some drivers.
- They can be configured from Windows Security as well as through Registry, App Control, PowerShell, and corporate policies.
- Tools such as Win32_DeviceGuard and msinfo32 allow you to check the status of VBS and diagnose problems in physical and virtual environments.
If you use Windows 11, you've probably seen the option at some point to core isolation and memory integrity within Windows security And yet, you might not be entirely sure what it does exactly or whether you should even activate it. This isn't unusual: it's one of those powerful security features that Microsoft has been incorporating in recent years, but which are poorly explained and often get buried deep within the menus.
Additionally, you may have encountered the typical message that you cannot turn on memory integrity because there are incompatible controllersOr perhaps the switch appears grayed out and you don't know where to begin. Between BIOS, virtualization, VBS, drivers, WMI, and other jargon, it's easy to get confused. Here, we'll break it all down calmly, in plain English, so you know what it is, how to activate it, what to do when it gives errors, and in what cases it's worth having it turned on or off.
What is kernel isolation in Windows 11?
Core insulation is a layer of security that takes advantage of hardware virtualization functions to create a protected area within the system's memory. This sort of "bubble" is used to run sensitive Windows processes in isolation from the rest of the operating system, drastically reducing the possibility of malware accessing areas it shouldn't.
In practice, Windows uses the hypervisor (the same basic mechanism used by virtual machines) to create a specialized virtual environment that acts as root of trustThe system assumes that, in the worst case scenario, the kernel could be compromised, so it places certain security checks within that shielded environment, not in the kernel itself.
It's important to understand that this isolation focuses on keeping critical operating system processes separate from devices or drivers that could be an attack vector. This is achieved by running these sensitive components within virtual memory. separate from the rest of the processesIt is extremely difficult for malicious code, even if it manages to execute, to alter basic security mechanisms.
This technology is part of the set of features of virtualization-based security (VBS) which Microsoft has been promoting for years. VBS is not exclusive to Windows 11: it is also available in Windows 10 and in Windows Editions of Windows Server modern, but in Windows 11 it has taken on a more prominent role because security is one of the pillars of the system.
What is memory integrity and how does it fit into all of this?
Memory integrity, also known as Hypervisor-Enforced Code Integrity (HVCI), is a key component of kernel isolation. Its role is to ensure that the code integrity process which is responsible for validating that what is executed in kernel mode does so within that secure virtual environment created by VBS, and not directly in the "bare" kernel.
This mechanism protects both the operating system and other security components from any malware attempt to modify code integrity rules. Because it runs in a hypervisor-protected bubble, it is extremely difficult for an attacker to alter or bypass these checks without being detected.
An important function of memory integrity is the protection of Control Flow Guard (CFG) bitmap For kernel-mode drivers, CFG helps mitigate attacks that attempt to divert a program's execution flow; by safeguarding this map in a secure virtual environment, it prevents a malicious (or compromised) driver from modifying it to force unwanted executions.
It also safeguards the kernel's code integrity process itself, ensuring that trusted kernel processes have valid certificates and that this validation cannot be manipulated. In other words: it acts as a security guard that monitors which controllers and code can enter kernel mode and ensures that no one changes the rules mid-game.
It's important to emphasize that memory integrity doesn't replace antivirus software. It's a complement: it works alongside Windows Defender (or whatever solution you use) to strengthen the system's core. Defender remains responsible for detecting and blocking malware at the file, process, network, etc., level, while memory integrity focuses on protecting the... kernel and high-security processes.
Advantages and disadvantages: safety versus performance
Enabling kernel isolation and memory integrity provides a significant security improvement, but it's not all free: it has some drawbacks. side effects on performance and compatibility that should be considered depending on how you use the equipment.
On the positive side, this feature helps protect the system against threats that attempt to directly attack the kernel or code validation mechanisms. It is especially useful in environments where various websites are accessed, numerous files are downloaded, or programs are installed from untrusted sources. It also fits very well in shared or public computers, such as office computers, classrooms, libraries or cybercafés.
The cost arises because every time the system has to validate kernel-mode code, the process must go through that series of checks within the secure virtual environment. It's as if every time you enter your house, in addition to opening the door with your key, you also had to... security guard They check your documents and make sure you're not carrying anything dangerous. You gain security, but it takes longer to get in and the guard uses up resources.
On powerful systems, this is usually barely noticeable in everyday use, but on machines with limited resources, modest laptops, or handheld consoles running Windows 11, the impact on smoothness and FPS can be quite significant. It's no coincidence that, on these types of devices (Lenovo Legion Go, Asus ROG Ally, and similar models), one of the most frequently repeated pieces of advice for scratch off extra performance to disable core isolation.
Furthermore, some older or poorly designed drivers and applications don't work well with these technologies. They may fail to load, cause blue screens, or lead to instability. Therefore, while Microsoft recommends keeping these features enabled whenever possible, it also allows you to disable them and offers advanced configuration options for businesses and administrators.
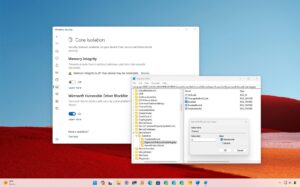
How to enable kernel isolation and memory integrity from the graphical interface
For most home users, the easiest way to enable these features is through Windows Security, without touching the Registry or anything unusual. The steps are quite straightforward, both in Windows 11 and Windows 10.
In Windows 11, you can follow this basic path using system settings:
1. Press the Windows key + I to open the Settings app. You can also click the Start button and then the Settings gear icon.
2. In the menu on the left, go to the "Privacy and security" section.
3. Inside, select "Windows Security".
4. Press the "Open Windows Security" button to launch the classic security panel.
5. In the side menu, click on "Device Security".
6. Locate the "Core Isolation" block and click on "Details".
7. On that screen you'll see the "Memory Integrity" option. If the control is disabled, slide the switch to turn it on. activate it.
8. Close the window and restart your computer for the changes to take effect.
In Windows 10, the process is very similar, although some menu names are slightly different. You would start with the Windows + I key combination, then go to "Update & Security," enter "Windows Security," and from there, go to "Device Security" and "Kernel Isolation Details" to enable or disable memory integrity as needed.
The good thing is that this function can turn on and turn off As many times as you like. For example, you can keep it active normally, and if you're going to use a very demanding program that you know will cause performance drops, or a specific game where you're experiencing low FPS, temporarily disable it and then re-enable it later. It's also a good idea to enable it when you connect USB drives of unknown or unreliable origin.
Advanced activation via Windows Registry and VBS
In professional environments or when you want to have minute control over how VBS behaves and memory integrity, you can use the Windows' register and other management tools. This allows you to automate activation on many devices or adjust options such as UEFI lock or mandatory mode.
The main configuration path for VBS and memory integrity is located under the key:
HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard
A recommended configuration to enable VBS and memory integrity without forcing UEFI locking can be applied with a series of reg add commands executed in a command prompt or PowerShell with administrator privileges. These commands activate the virtualization-based securityThey define the platform's security requirements (such as Secure Boot and DMA protection), establish whether the system is locked at the UEFI level, and turn on the hypervisor-enforced code integrity scenario.
For example, you can:
- Enable VBS only without memory integrity by adjusting the value EnableVirtualizationBasedSecurity and 1.
- Indicate that only Secure Boot is required by setting RequirePlatformSecurityFeatures in 1.
- Require both Secure Boot and DMA protection with a value of 3 in that same key.
- Define whether UEFI locking is desired or not using the value Locked (0 for no lock, 1 for lock).
- Enable memory integrity by configuring Enabled in the DeviceGuard\Scenarios\HypervisorEnforcedCodeIntegrity branch.
There is also the possibility of enabling VBS and memory integrity in mandatory mode using the Mandatory value. In this scenario, if the hypervisor, the secure kernel, or any of its critical components fail to boot, the operating system loader does not continue with the normal boot process, thus preventing the computer from starting in a potentially unsafe state.
There is also an interesting key for controlling the graphical interface for memory integrity: WasEnabledByDeleting it using reg delete causes the option to appear grayed out in the Windows Security app with the message "This setting is managed by your administrator". However, setting it as a DWORD 2 value restores the interface's normal functionality, allowing the user to interact with the switch.
Using App Control to enable memory integrity
In managed organizations and environments, it is common to use App Control for Business (Enterprise Application Control) to configure security policies, including enabling memory integrity through centralized rules.
There are several ways to use App Control to enforce hypervisor-protected code integrity. One of the simplest is to use the Application Control Wizard provided by Microsoft. When creating or editing a policy, on the wizard's policy rules page, you can enable the option to integrate Hypervisor-Protected Code Integrity as part of the configuration.
Another alternative is to use PowerShell with the cmdlet Set-HVCIOptionsThis allows for more granular modification of HVCI-related options. This method is very useful when integrating changes into automated deployment scripts or configuration pipelines.
Finally, more advanced administrators can directly edit the App Control Policy XML and adjust the value of the element In this way, it is possible to explicitly define how and when memory integrity should be applied to the computers that receive this policy, integrating the configuration with other security requirements of the organization.
How to check if VBS and memory integrity are active
Once everything is configured, it's important to verify that VBS and memory integrity are actually working on the system. Windows offers several tools for this, both command-line and through graphical interfaces. For more detailed testing, you can consult the [link/reference/etc.]. security audit guide.
One of the most flexible options is to use the WMI class Win32_DeviceGuardAvailable in Windows 10, Windows 11, and Windows Server 2016 and later. From an elevated Windows PowerShell session, you can launch:
Get-CimInstance -ClassName Win32_DeviceGuard -Namespace root\Microsoft\Windows\DeviceGuard
The output of this command displays various properties related to virtualization-based security and memory integrity. Among the most relevant are:
- InstanceIdentifier, which uniquely identifies each device.
- Version, which indicates the version of the WMI class (currently 1.0).
- AvailableSecurityProperties, where the security features supported by the hardware are listed, such as hypervisor compatibility, secure boot, DMA protection, secure memory overwrite, NX protections, SMM mitigations, MBEC/GMET or APIC virtualization.
In addition, there are other fundamental fields for understanding the state of the system:
- CodeIntegrityPolicyEnforcementStatus: indicates whether the code integrity policy is disabled, in audit mode, or in strict compliance mode.
- RequiredSecurityProperties: lists which security properties are necessary to enable VBS, such as hypervisor support, Secure Boot, DMA protection, etc.
- SecurityServicesConfigured: indicates whether services such as Credential Guard, memory integrity, secure boot system protection, SMM firmware measurement, or kernel-mode stack protection have been configured.
- SecurityServicesRunning: reports which security services are actually running at that time.
It is also interesting to look at VirtualizationBasedSecurityStatusThis clarifies whether VBS is not enabled, if it is enabled but not running, or if it is enabled and running. Other fields such as SmmIsolationLevel, UsermodeCodeIntegrityPolicyEnforcementStatus, VirtualMachineIsolation, and VirtualMachineIsolationProperties complete the overall picture of the system's security status, including advanced virtual machine isolation scenarios.
If you prefer something visual, you can use the graphics tool. msinfo32.exeBy opening it from an elevated privilege session, in the "System Summary" section you will find, at the bottom, information about the available and active virtualization-based security features, including the status of kernel isolation and other related functions.
Common problems and how to solve them
One of the most common errors when trying to enable memory integrity is that Windows warns of incompatible controllersSometimes, clicking on "Check for incompatible drivers" displays specific listings (usually .sys or .inf files), but other times the user finds that nothing is shown, which makes identifying the culprit quite difficult.
To get out of this predicament, the first thing to do is to make sure that the hardware is compatible with the necessary virtualization functions and that the Virtualization is enabled in the BIOS/UEFIWithout hypervisor support and without these options enabled, VBS and memory integrity will not function correctly.
From there, it's highly recommended to check and update all important drivers: chipset, graphics, storage devices, network, etc. Manufacturers usually release newer versions that are compatible with the enhanced integrity policies or that fix compatibility issues with VBS in Windows 11.
When drivers are particularly old or of dubious origin, updated versions may not be available in Windows Update or on the manufacturer's website. In such cases, it's necessary to consider... uninstall completely Identify the problematic driver and replace it with a generic or modern alternative. Sometimes, it's necessary to use Device Manager, show hidden devices, and review each suspicious driver individually.
If a driver fails to load or causes runtime crashes after enabling memory integrity, another approach is to check for a properly signed version adapted to this environment. If none exists, it may be wiser to forgo that specific hardware or software rather than leave the system exposed.
System recovery if something goes wrong
Although it's not common, enabling VBS and memory integrity can sometimes cause the computer to behave erratically, with critical startup errors or recurring blue screens. In such cases, it's important to know how to revert to these settings without losing control of the machine.
The first thing to do is disable any group policy or policy that was used to force the activation of VBS and memory integrity. If there is a GPO, startup script, or MDM policy pushing that setting, it must be reverted to prevent the system from reapplying it after recovery.
Then, the computer can be started in the Windows Recovery Environment (Windows RE)From there, you have access to advanced options that allow you to open a console, restore the system, uninstall updates, or modify the Registry without booting into the main Windows environment, which is very useful when the problem prevents a normal startup. Before modifying the Registry, perform a Registry backup.
Once inside Windows RE, you can directly change the value that controls memory integrity in the Registry. For example, you can set the Enabled value of the HypervisorEnforcedCodeIntegrity key to 0 to disable it. After making that adjustment, you would simply need to reboot the device so that the system would restart without the problematic function.
These types of maneuvers should be done with some care, but they are an effective way when the equipment is trapped in a faulty boot loop due to an incompatible driver or a bad combination of hardware and security policies.
Memory integrity in Hyper-V virtual machines
Memory integrity is not limited to physical equipment. It can also protect virtual machines Created with Hyper-V, this provides an additional layer of security for guest systems. The steps to enable it from within the virtual machine are very similar to those on a physical machine: configure VBS, activate kernel isolation, and turn on memory integrity from Windows Security.
In this scenario, memory integrity protects against malware running within the guest virtual machine, just as it would on a physical PC. However, it does not protect the VM from the host administrator. The Hyper-V administrator always retains the ability to disable memory integrity for a specific virtual machine, for example, using the Set-VMSecurity command with the VirtualizationBasedSecurityOptOut option.
For all of this to work, the Hyper-V host must meet certain requirements. minimum requirementsYou need to be running at least Windows Server 2016 or Windows 10 version 1607, as earlier versions do not have all the necessary components for VBS in guest environments. Additionally, the virtual machine must be a Generation 2 virtual machine and run at least Windows Server 2016 or Windows 10.
It is possible to enable memory integrity and the nested virtualizationThis allows the Hyper-V role to be installed within the VM itself, enabling the creation of more virtual machines. To do this, the Windows nested virtualization environment must first be prepared on that machine.
There are some important limitations to consider: Virtual Fibre Channel adapters do not support memory integrity, so before connecting them to a VM, you must exclude it from virtualization-based security using `Set-VMSecurity`. The `AllowFullSCSICommandSet` option is also not supported on pass-through disks when using memory integrity; if you need this option, the machine must be excluded from VBS.
In summary, memory integrity can also play a key role in virtualized environmentsprovided that the hardware and configuration restrictions of Hyper-V are respected.
Ultimately, kernel isolation and memory integrity in Windows 11 form a powerful combination for increasing system security, especially against sophisticated kernel-targeting attacks. However, they come with conditions: you need compatible hardware, you should expect some performance impact, and you must be prepared to deal with drivers that aren't a perfect fit. If you primarily use your PC for browsing, managing documents, connecting to corporate networks, or handling sensitive data, it makes a lot of sense to keep these features enabled, and you should check out our security secretsIf your absolute priority is to squeeze every frame out of games or to get the most out of a computer with limited resources, you might prefer to disable them or alternate them depending on how you're going to use them at any given time.
Passionate writer about the world of bytes and technology in general. I love sharing my knowledge through writing, and that's what I'll do on this blog, show you all the most interesting things about gadgets, software, hardware, tech trends, and more. My goal is to help you navigate the digital world in a simple and entertaining way.