- Windows Server 2025 hardens credentials, Active Directory, SMB, and networking by default, relying on VBS, Credential Guard, and a revised security baseline.
- Improvements to Hyper-V, ReFS storage, Dev Drive, and GPU-P enable support for high-demand workloads, AI, and complex hybrid scenarios.
- Azure Arc, SDN, and SMB over QUIC integrate the server with the cloud and facilitate Zero Trust models and secure access for remote work and distributed environments.
- Pentesting tests show that many classic climbing routes fail, but safety still depends on careful setups and good practices.
Windows Server 2025 arrives with a very serious leap in securityIdentity management, performance, and hybrid cloud capabilities. This isn't a simple incremental update: Microsoft has addressed virtually every layer of the system, from the kernel to Active Directory, including SMB, Hyper-V, storage, and preconfigured hardening policies. If you manage on-premises or hybrid infrastructures, it's worth understanding what's changed and how to leverage it.
In parallel, Windows Server 2025 hardens many classic attack vectors from the factory.Credentials stored in memory, insecure protocols, outdated encryption, and uncontrolled exposed services are all issues addressed. It also introduces new tools for remote administration, automation, and observability that, combined with best practices, allow you to build architectures close to the Zero Trust model without driving yourself crazy on a daily basis.
Desktop experience and base server environment
Even though we're talking about a server-oriented system, the user experience layer also changes.After logging into Windows Server 2025 for the first time, you'll find a desktop very much in line with the visual style of Windows 11, with a modernized interface, a redesigned Task Manager with Mica material, and a more polished overall experience.
In-place upgrades are also made more flexibleYou can jump directly to Windows Server 2025 from Windows Server 2012 R2 and later versions, allowing up to four version jumps in a single operation. This greatly simplifies the migration of older environments that weren't ready to upgrade to 2016, 2019, or 2022.
Integrated connectivity capabilities are expandedThe server now includes wireless LAN service as standard; you only need to activate the service with net start wlansvc to provide Wi-Fi, and adds Bluetooth support for mice, keyboards, headphones and other devices, which is useful in labs, POCs or physical environments that are not so "data center".
Among the tools for administrators, the arrival of Windows Terminal and WinGet stands out.These are installed by default. The Terminal allows you to work with multiple shells (PowerShell, CMD, SSH) in tabs, while WinGet provides a very convenient command-line package manager for installing, updating, and maintaining tools on servers, including process inspection tools such as Using Process Hacker on Windows.
Integration with services and accounts is also strengthenedFrom Settings > Accounts > Email and accounts you can add Microsoft Entra ID (formerly Azure AD), Microsoft accounts and professional or educational accounts, maintaining the classic domain link as the main pillar but opening the door to more hybrid scenarios.
Multi-layer security and native hardening
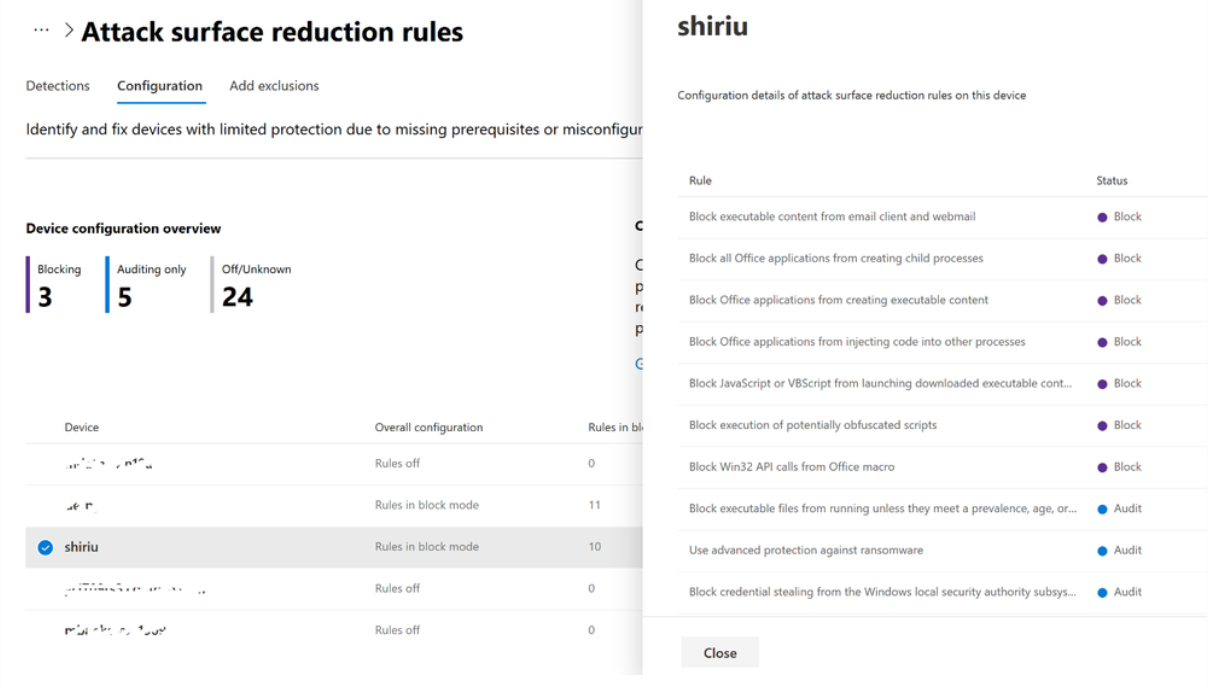
Windows Server 2025's main focus is on in-depth security.Microsoft is hardening default settings, publishing frequent security baseline updates, and adding new technologies to protect credentials, communications, and exposed services, with a particular focus on ransomware attacks and privilege escalation.
Updated security baseline and refined policies
The official security baseline for Windows Server 2025 (v2506 and later) is reviewed more frequently to adapt to new threats and community feedback. Among the most relevant adjustments are changes to remote login rights and advanced auditing.
Microsoft modifies the SeDenyRemoteInteractiveLogonRight policy to use the SID S-1-5-114 (local accounts that are also administrators) instead of the generic SID S-1-5-113 (all local accounts). This keeps RDP access to local accounts with high privileges blocked, but leaves room for local accounts without the admin role that can be used in support or recovery scenarios when the domain is unavailable.
The Guests group is also added to the "Deny login using Remote Desktop Services" policy.So, even if the Guest account is activated by mistake, it still won't be able to access via RDP. This is an extra layer of defense against incorrect configurations or legacy GPOs.
Some historical directives are removed from the baseline because they are obsolete or irrelevant.For example, the policy “WDigest Authentication (disabling might require KB2871997)” is removed because WDigest itself no longer stores passwords in plain text in current versions, and “Allow Windows Ink Workspace” is removed as it does not apply to servers, reducing noise and GPO processing time.
In parallel, visibility is increased with new auditing options.The auditing of “authorization policy change (Success)” is enabled on Domain Controllers and Member Servers to log critical modifications to user rights and security policies, and command-line capture is enabled for process creation events, which greatly improves detection capabilities in SIEM and EDR, as explained in the security audit with auditpol and wevtutil.
Virtualization-based security, Credential Guard, and protected LSA
Virtualization-based security (VBS) is becoming established as one of the pillars of modern hardening.It leverages hardware virtualization to create an isolated environment that protects critical components from the operating system itself, drastically hindering credential theft and memory manipulation attacks.
Credential Guard is now enabled by default on eligible devicesThis feature moves NTLM secrets, Kerberos TGT tickets, and Credential Manager credentials to a separate VBS environment, so that not even an attacker with local administrator privileges can read them in memory using tools like Mimikatz.
To confirm the status of this protection you can use PowerShell with consultations to the class Win32_DeviceGuard, reviewing the values of SecurityServicesConfigured y SecurityServicesRunningand verify LSA insulation by checking the value RunAsPPL in the registry. A value of 1 indicates that LSASS is running as a Protected Process (PPL).
The baseline also highlights the role of two policies closely linked to the UEFI blockadeActivating VBS (Device Guard) and configuring LSA as a protected process are key security measures. When combined with Secure Boot, TPM 2.0, and firmware that locks UEFI variables, these protections become very difficult to disable, even for local administrators. However, it's advisable to validate hardware compatibility and plan carefully, as reversing these measures isn't always straightforward. For a better understanding of concepts related to VBS and physical system isolation, the documentation on [topic missing in original text] is helpful. core insulation.
Hardened and more scalable Active Directory
Active Directory receives one of the biggest facelifts in recent years, both in terms of performance and cryptographic security and default behavior towards legacy clients and controllers.
First, a 32k database page size option is introduced. For AD DS and AD LDS. Until now, the ESE database worked with 8k pages, which imposed limits on the size of objects and multi-value attributes. With 32k pages, multi-value attributes can grow approximately 2,6 times larger, and several historical scalability constraints are alleviated. The migration requires that all domain controllers in the forest support this new format.
The Active Directory schema is also being expanded with new LDF files (sch89.ldf, sch90.ldf, sch91.ldf and their equivalent in AD LDS MS-ADAM-Upgrade3.ldf), adding classes and attributes for the new security and management functions. In addition, an object repair function is incorporated (fixupObjectState) to restore critical attributes such as SamAccountType u ObjectCategory in damaged objects.
Team account password security is being strengthenedMachine accounts now receive random passwords by default, and Domain Controllers 2025 block the use of the typical password that matches the account name. A new GPO, "Domain Controller: Reject machine account default password setting," allows you to manage this behavior, and tools like ADAC, ADUC, or commands net computer y dsmod They respect this new policy.
Multiple cryptographic and protocol aspects are reinforced, especially in Kerberos and LDAPRC4 is disabled in TGTs, and the legacy registration key is no longer used. SupportedEncryptionTypes In support of Group Policy Objects (GPOs), PKINIT is updated to support more modern algorithms, and TLS 1.3 support is introduced in LDAP. Additionally, encryption is required for operations with sensitive attributes, and LDAP signing (sealing) is enforced by default in new implementations.
Operational improvements include NUMA support, new performance counters, and advanced replication control.AD DS can now take advantage of all processor groups beyond 64 cores, incorporates specific counters for the DC Locator, LSA (names/SID) lookups and LDAP client, and allows increasing replication priority with certain partners for specific scenarios.
Delegated Managed Service Accounts (dMSA) and Enhanced LAPS
One of the major new developments in service identity management is Delegated Managed Service Accounts (dMSA)This new type of account allows you to migrate traditional service accounts to identities with fully randomized, automatically managed keys, without drastically changing the application. Original passwords are disabled, reducing attack surfaces and enabling more granular administrative delegation.
The integrated Windows LAPS solution also takes a significant leap forward. In Windows Server 2025, LAPS generates and rotates unique passwords for each local administrator, securely storing them in AD or Microsoft Entry ID, but now adds features such as new automatic local account management, image rollback detection using the attribute msLAPS-CurrentPasswordVersion and support for human-readable passphrases EatYummyCaramelCandy.
A new, "more readable" password complexity is introduced. (value 5 in PasswordComplexityThis excludes easily confused characters such as I/O/Q/l/0/1 and certain symbols, maintaining robustness while reducing typing errors. The ADUC add-on includes an improved LAPS tab with more readable fonts for displaying passwords.
In addition, LAPS integrates new post-authentication actions (PAA), such as the option “Reset the password, sign out the managed account, and terminate any remaining processes”, which not only logs out the managed account after the reset, but also lists and terminates all processes that are still running under that identity, with expanded log events to facilitate auditing.
Hardened SMB: QUIC, encryption, signing, and brute-force mitigation
The SMB protocol is another key area receiving significant hardening., both at the transport level and in terms of authentication and access control, designed especially for hybrid environments and remote work.
SMB over QUIC becomes more widespread beyond Azure Edition It is available in Windows Server Standard and Datacenter. This mode encapsulates SMB 3.1.1 over QUIC using TLS 1.3 and UDP ports, creating a kind of "SMB VPN" for secure access to edge servers from untrusted networks, ideal for remote work and mobile devices without setting up a traditional VPN.
Administrators can control SMB over QUIC using GPO and PowerShellThe QUIC client can be disabled with the "Enable SMB through QUIC" policy or with Set-SmbClientConfiguration -EnableSMBQUIC $falseEnable signature and encryption audits to detect clients or servers that do not support these capabilities, and review the corresponding events in the SMBClient and SMBServer logs (Audit and Connectivity).
Alternative SMB ports are introduced for TCP, QUIC, and RDMAThis allows you to bypass the traditional TCP/445 port when your security design requires it. Firewall rules have also been updated: when creating new shared resources, NetBIOS ports 137-139 are no longer automatically opened; instead, a more restrictive rule group, "File and Printer Sharing (Restrictive)," is used. To check exposures and open ports on the server, you can consult guides for View open network ports.
In authentication, all outgoing SMB connections now require signing and encryption according to the configuration.The client can block NTLM for remote connections, and the SMB service implements an authentication rate limiter to curb NTLM- or PKU2U-based brute-force attacks, introducing increasing delays after failed attempts.
IPsec, RRAS and other connectivity hardening measures
Beyond SMB, Windows Server 2025 adjusts other network and VPN components to align them with modern cryptographic security standards.
In IPsec, the default key module order changes to IKEv2 and IKEv1 For authenticated connections using machine certificates, leaving AuthIP as a legacy option that can be reactivated with the registration key IpsecRestoreLegacyKeyModThis pushes organizations to use IKEv2, which is more robust and modern.
In Routing and Remote Access (RRAS), new installations come with PPTP and L2TP disabled. By default, they can still be enabled if the environment requires it, but the intention is to prioritize SSTP and IKEv2, which are much more secure. Configurations that already used PPTP/L2TP and are updated will maintain their behavior to prevent unexpected disconnections.
Windows strengthens minimum requirements for certificates and TLSCertificate search and management supports SHA-256 as standard, and TLS server certificates must use RSA keys of at least 2048 bits, aligning with the phase-out of certificates considered weak.
Hyper-V, performance, and infrastructure for AI
In the area of virtualization, Windows Server 2025 expands horizons both in raw performance and in support for artificial intelligence workloads., which increasingly rely on GPUs, massive memory, and low-latency networks.
Hyper-V significantly increases the limits of scalabilityNow a host can handle up to 4 PB of memory and 2048 logical processors, while a Generation 2 virtual machine can reach 240 TB of RAM and 2048 vCPUs, opening the door to huge database environments, advanced analytics, or local AI engines.
GPU partitioning (GPU-P) allows a single physical GPU to be shared among multiple virtual machines.GPU-P allocates dedicated "slices" based on the needs of each VM. This is key for AI, rendering, or compute-intensive scenarios where previously a GPU had to be dedicated per guest host. Furthermore, GPU-P supports high availability with automatic failover within the cluster and live migration, even with partitioned GPUs.
Dynamic processor compatibility is redesigned for mixed clusters, using the maximum set of CPU features shared across all nodes, improving performance over the classic compatibility mode, especially when using capabilities such as second-level address translation (SLAT).
The hypervisor forced pagination translation (HVPT) feature adds another layer of defense HVPT protects against arbitrary memory write attacks, safeguarding the system's key page table structures. HVPT is active by default when supported by the hardware, but not when the server is running as a guest virtual machine.
In virtual networks, the Accelerated Networking (AccelNet) feature is arriving in a preview version. To simplify the use of SR-IOV in clusters, reducing latency, jitter, and CPU usage, Network ATC offers an intent-based model for deploying consistent host network configurations across the cluster.
Modern and optimized storage for development
The storage subsystem in Windows Server 2025 is also being revamped, with improvements in NVMe performance, new ReFS capabilities, and optimizations geared towards developers and high-efficiency scenarios.
Dev Drive, already known in Windows 11, arrives in the server world Dev Drive is a ReFS-based volume type optimized for development workloads, offering finer control over filters, antivirus, and security settings. Now, Dev Drive also supports block cloning, enabling copies of large files to be performed as low-cost metadata operations, reducing actual I/O and significantly speeding up the process.
ReFS incorporates native deduplication and compression Designed for both static workloads (image repositories, backups) and active virtual desktops or file servers. In high-volume data environments, capacity savings can be very significant without significantly impacting performance.
Thin-provisioned volumes on Direct Storage Spaces facilitate more efficient capacity allocationThis allows for safe over-provisioning while monitoring actual consumption. Furthermore, it's possible to convert existing fixed volumes to thin volumes, returning unused space to the pool for reuse in other volumes.
In terms of pure performance, NVMe support is better tuned.This increases IOPS and reduces CPU usage compared to previous versions. SMB also incorporates compression with the LZ4 standard, adding another option to XPRESS, LZNT1, and PATTERN_V1 for scenarios where prioritizing compression and decompression speed is desired.
Azure Arc, hybrid model and centralized management
Windows Server 2025 fully embraces the hybrid model with Azure Arc, making it easier to manage on-premises servers as if they were native Azure resources, including billing, monitoring, and advanced operations.
The Azure Arc installer becomes an on-demand feature installed by default.With a very simple wizard and a system tray icon that speeds up the server connection to Arc. Once connected, you can apply policies, monitor, deploy extensions, or integrate with other Azure solutions in a unified way.
Pay-as-you-go licensing is being introduced through Azure ArcThis allows Windows Server to be licensed in subscription mode and to pay only for actual usage, an interesting alternative to perpetual licenses for environments with high load variability or projects of limited duration.
Azure Arc-enabled Windows Server management brings several added advantages: integration with Windows Admin Center directly in the Azure portal, Just-In-Time remote support with detailed logs, automated best practice assessments, and guided deployment of Azure Site Recovery for business continuity.
Software-Defined Networking and Azure-like security policies
Software-defined networking (SDN) in Windows Server 2025 is getting even closer to the Azure experience., both in operating model and in default protections.
The SDN network controller is now hosted as a cluster service on physical hosts, eliminating the need to deploy dedicated virtual machines for this component, simplifying the topology and freeing up computing resources.
Default network policies are introduced with a "deny by default" philosophy.Similar to Azure Network Security Groups: all incoming traffic to the load virtual machines is initially denied, opening only the explicitly allowed ports, while outgoing traffic is allowed by default so as not to slow down applications.
Service labels allow for more intuitive segmentation of workloads.Associating NSGs with virtual machines using human-readable labels instead of IP ranges makes it easier to change topologies without rewriting complex rules and reduces configuration errors.
SDN Multisite functionality provides L2 and L3 connectivity between different locations without additional components.Maintaining unified policies even when virtual machines migrate between sites. This is complemented by improved performance from Layer 3 gateways, which consume less CPU and offer greater throughput.
Container portability and the Windows Server Insider Program
In containers, Windows Server 2025 focuses on portabilityThe platform allows moving container images and their data between different hosts and environments without changes, reducing friction when updating host versions or changing infrastructure.
This portability simplifies the modernization of legacy applications.This is because you can encapsulate them in Windows containers and move them between on-premises, public clouds, or test environments without having to repackage each time, as long as you respect the minimum version compatibility.
To stay up to date on these capabilities, the Windows Server Insider Program It offers early access to builds with new features and changes, allowing administrators and partners to test security, performance, and compatibility scenarios before they reach production.
Update status, known issues, and real-world security testing
Windows Server 2025, like any living system, has a constant cycle of updates and fixes.Microsoft documents known issues and their resolution status quite transparently.
Among the recent incidents, a glitch with WUSA stands out. Installing .msu files from shared resources with multiple packages generated errors ERROR_BAD_PATHNAMEMitigation involves copying the .msu files locally or using Known Issue Rollback (KIR) with special group policies, while a definitive fix is distributed in future updates.
Another issue affected machine password rotation when using Kerberos authentication with PKINITThis caused some devices to be left with expired passwords and authentication failures. It was fixed in the April 2025 security update (KB5055523), and in the meantime, the Credential Guard Team Accounts feature was temporarily disabled until a stable solution was available.
There were also reports of unexpected updates from Windows Server 2019 and 2022 to 2025. In environments with third-party patch management tools that treated feature updates as recommended rather than optional, Microsoft mitigated the situation by pausing the offer banner in Windows Update and working with vendors to clarify the use of the DeploymentAction=OptionalInstallation classification.
Beyond theory, penetration testing laboratories have put the new protections to the test.In tests with various Potato-type tools (Juicy, Lovely, Rogue, PrintSpoofer), most failed, while PetitPotato only managed to escalate to the local Administrator level, not to SYSTEM. This indicates a real strengthening of impersonation controls and COM/RPC services, although it remains vital to review service configurations and file permissions.
Escalation tests using misconfigured services, such as DNSadmin attacks or FTP abuse, remain viable. If basic permission errors are made, it's a reminder that not even the best operating system can compensate for poor configuration; it's advisable to use utilities to audit permissions and paths such as Using AccessChk in Windows and review access controls.
Attempts were also made to exploit kernel vulnerabilities such as CVE-2025-21325, without success in updated builds, where the exploit caused BSODs due to KERNEL_SECURITY_CHECK_FAILURE instead of escalating to SYSTEM.
Overall, Windows Server 2025 takes security by design to a significant leap forward.It reduces credential exposure, hardens protocols, and introduces a more aggressive baseline without sacrificing operational flexibility, combining on-premise, hybrid, and AI capabilities so that organizations can build more resilient, monitorable, and threat-ready infrastructures, provided they accompany this with good practices, regular audits, and a clear hardening strategy.
Passionate writer about the world of bytes and technology in general. I love sharing my knowledge through writing, and that's what I'll do on this blog, show you all the most interesting things about gadgets, software, hardware, tech trends, and more. My goal is to help you navigate the digital world in a simple and entertaining way.