- The U2F and FIDO2 USB security keys add a physical factor that blocks phishing attacks and password theft.
- It is possible to use anything from USB flash drives with software like USB Raptor to Pico Fido-type projects or devices like Flipper Zero.
- Services like Google, Dropbox, or GitHub allow you to register U2F/FIDO2 keys and combine several with recovery methods.

La security of our online accounts It's become a serious issue: we frequently hear about massive data breaches, password thefts, and increasingly sophisticated attacks. If you use Gmail, social media, cloud services, or handle sensitive information, relying solely on a simple handwritten password is, frankly, playing with fire.
In this context, the following have gained considerable importance: USB security keys based on U2F and FIDO2These are tiny physical devices that connect to your computer or mobile phone and serve as a second (or even sole) login method. Let's see exactly what they are, what types exist, how you can create your own security key (from a simple USB drive to projects like the Raspberry Pi Pico or even Flipper Zero), and how to integrate them with services like Google, Dropbox, or GitHub.
What is a USB security key and how does U2F fit in?
When we talk about a USB security key, we are referring to a physical device that serves as a second verification step When you log into your accounts. In other words, a username and password are no longer enough: to complete access, the system asks you to connect that key and, usually, press a button or confirm the operation.
This system falls within the two-step authentication or two-factor verification (2FA)It combines something you know (your password) with something you have (the physical key). So, even if someone figures out your password, they still won't be able to get in because they lack the device you have in your pocket or on your keychain.
The most widespread nowadays are the keys that use the standards U2F (Universal 2nd Factor) and FIDO2Developed by the FIDO Alliance with support from companies like Google and Yubico, these protocols allow browsers and operating systems to recognize the key as a secure and standard authentication method, compatible with services such as Google, Dropbox, GitHub, Facebook, Nextcloud, Opera, and many others.
The beauty of this approach is that You don't depend on SMS, calls, or emails For the second step. This way you avoid many phishing attacks and techniques like SIM swapping, and you also simplify the process: you connect the key, confirm and that's it, without having to copy codes.
Why passwords are no longer enough
For years, the only shield has been the traditional password stored on the serverThe problem is that most users reuse passwords, use weak combinations, or fall into phishing traps where they hand over their password on fake pages that are almost identical to the official ones.
Two-step verification was created to put a stop to this: In addition to the password, the service asks you for an extra code that you receive via SMS, call, email, or authenticator app. So, even if someone steals your password, they would still need access to your mobile phone or email inbox.
However, attackers have taken it a step further. Today, it's common for a cybercriminal to set up a cloned website from Google, Facebook or another service They might also ask for the verification code you just received. If you fall for it and enter it, you're giving it to them in real time, and they can open your account in seconds.
That's where physical keys truly shine: They completely eliminate the concept of "code that you can read and rewrite"By using public-key cryptography, the browser and the key communicate directly, and you don't have anything to copy, so the attacker has nothing to steal from you through a fake website.
Types of security keys: buy or create your own
If we reduce the categories to the minimum, we can divide security keys into two main groups: the commercial keys that you buy ready-made and those you can assemble yourself with generic hardware or with a simple USB and specialized software.
Among commercial keys, the best known are the YubiKey, Google Titan, and other compatible FIDO keysThey come with a classic USB-A connector, USB-C, NFC for mobile devices, and even Bluetooth for wireless use. Their main advantage is that they are ready to work on multiple systems and browsers with minimal configuration.
On the other side are the "Homemade" or DIY keysThis involves using a standard USB drive or a microcontroller (Raspberry Pi Pico, ESP32, etc.) and loading it with firmware or software that acts as a security layer. In this case, the software itself monitors whether the USB drive is connected and uses it as an additional authentication factor, typically to protect your computer's login.
Both approaches have pros and cons: Commercial keys are more robust, smaller, and more secure.but also more expensive; homemade solutions are usually cheap or even free if you already have the hardware, but they depend heavily on the operating system configuration and, in general, do not reach the same level of certified security.
How to create a security key with a USB drive in Windows (USB Raptor)
If what you want is use a USB flash drive as a bootable USB driveIn Windows, there are specific programs that turn a regular USB drive into a login requirement. It's not exactly a standard U2F key for online services, but it does add a very useful layer of physical security to your computer.
One of the best-known projects is USB RaptorThis open-source tool links Windows locking and unlocking to the presence of a special file on your USB drive. While the drive is connected, you can use your computer; if you remove it, the system locks.
The basic operation is simple: Download the Raptor USB drive from its official website and extract it., without traditional installation. Next, connect the USB drive you want to use as a key and run the file “USB Raptor.exe”.
The first time you open it, several windows will appear. You will have to authorize access in the Windows Firewall so that you can communicate correctly with the system, and then accept the program license, where you can also choose the Spanish language for easier navigation.
Within the application, you'll see that the assistant is divided into three clear steps. First, you must define an encryption password This will protect the key file that will be created on your USB drive. Then, select the drive letter corresponding to the USB drive and click on “Create k3y file” to generate the special file that will act as a key.
Once the file already exists on the USB drive, all that remains is Activate the protection by selecting the “Activate USB Raptor” optionFrom that moment on, the computer will be associated with that key: when you remove it, the computer will lock, and to unlock it you will have to reconnect the memory (or use the emergency password you have set).
In the advanced settings, which are highly recommended, you can adjust details such as I want USB Raptor to run automatically when Windows starts, and to do so already activated.so that the system is protected from the first second and does not depend on you remembering to open the program each time.
Assembling a YubiKey-style FIDO2 key with a Raspberry Pi Pico (Pico Fido)
Commercial keycaps like YubiKey or Google Titan cost around 30 euros or more in their basic versionsIdeally, you should have at least two drives (one for daily use and another as a backup) so you're not stranded if you lose the main one. If you're on a tight budget, this might be a deterrent.
However, there is a very curious and economical alternative: the project Pico Fidowhich allows you to transform a Raspberry Pi Pico or ESP32 type microcontroller into a FIDO2 compatible security key, mimicking the behavior of a YubiKey for a fraction of the price.
These devices, originally designed for home automation and electronics projects, can be found in online stores for under 3 eurosThe recommended model is usually the original Raspberry Pi Pico, although there are variants with an integrated USB connector, such as some RP2040 modules shaped like a USB drive, or even more advanced versions like the Raspberry Pi Pico 2 RP2350 from Waveshare, which adds security improvements.
The process to convert one of these microcontrollers into a security key involves flash a specific firmwareDownload the image from the developer's website, connect the device to the PC in bootloader mode (usually by holding down a boot button when plugging it in) and copy the firmware file to the drive that appears on your system.
In the case of using an ESP32, the project itself Pico Fido offers a browser-based flashing toolwithout needing to install any additional utilities. Simply follow the wizard to flash the correct firmware onto the chip.
Once the firmware is installed, the key step arrives: using the tool called CommissionerThis software changes the device identifier and configures it so that Windows, Android, iOS, and browsers recognize it as an authentic key, for example by "simulating" a real YubiKey.
At Commissioner you can also activate security features such as Secure Boot or Secure LockYou can adjust the LED behavior and generally prepare the key to start registering passkeys for your online services. The advantage is that this entire process can be done directly from your browser, which greatly simplifies the setup for less advanced users.
After these steps, you will have Your own functional FIDO2 key for just a few euros, ready to store access keys and be used as an authentication device on a bunch of FIDO2 and U2F compatible websites, just like you would with a commercial YubiKey.
Passkeys and physical keys: the passwordless future
In recent years the concept of passkeys or passwordless access keysDriven by the FIDO Alliance itself and giants like Google, Apple, and Microsoft, the idea is simple: instead of remembering and typing passwords, passkeys are unique cryptographic keys linked to your devices or a physical key.
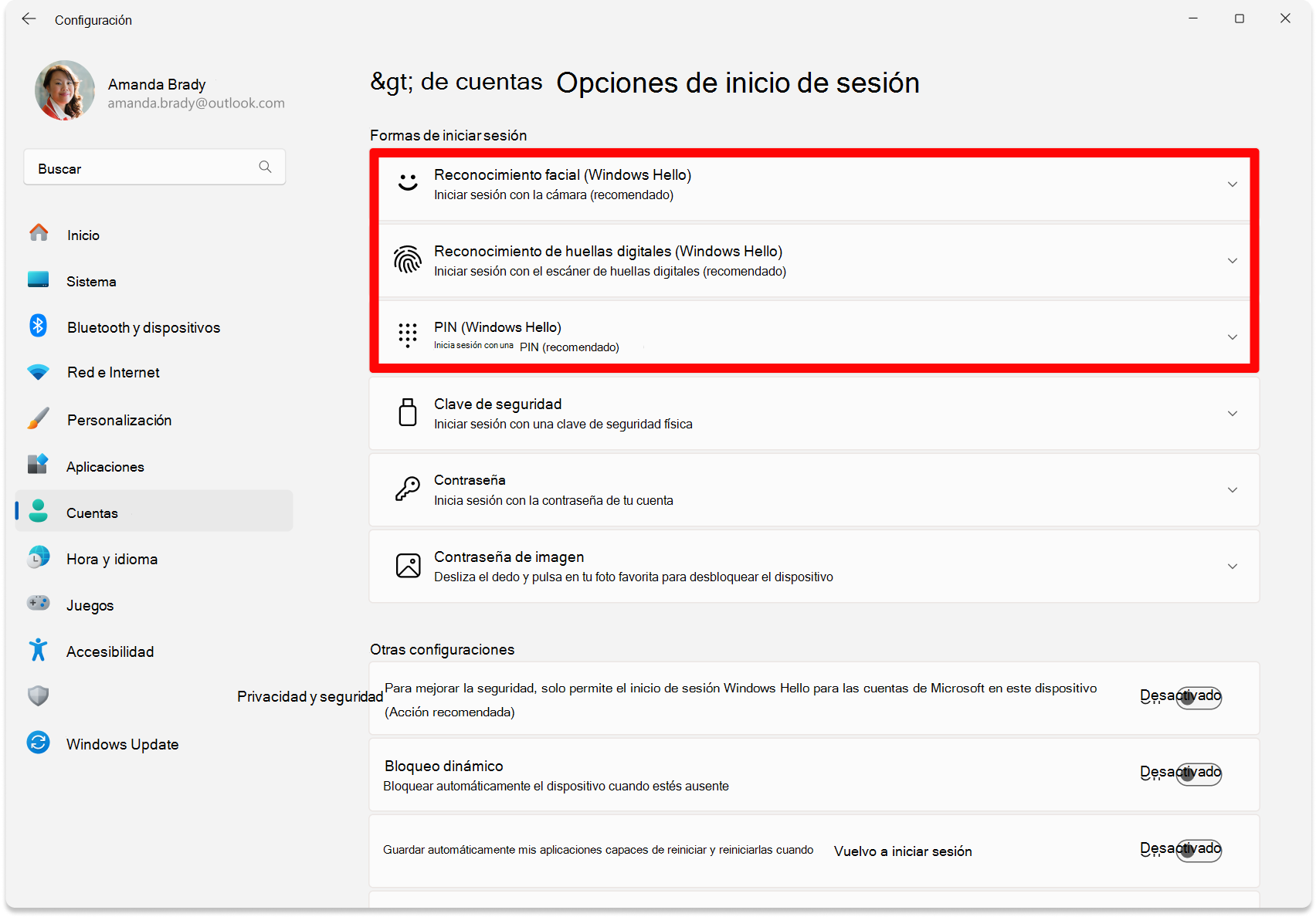
A passkey securely contains All the information you need to log in In a service: credentials, association with your user, and other parameters. When you visit a website that supports passkeys, you choose the corresponding access key stored on your device or key, validate it (with PIN, fingerprint, face, physical button, etc.), and enter directly, without seeing or typing passwords.
These passkeys can be stored in different locations: Android phones and iOS, Windows computers, operating system-specific keychains and even password managers like Bitwarden. While it's convenient to store them on your phone or computer, you lose some of the advantage of isolating your passwords on a dedicated physical device.
Originally, the concept was designed with specific devices like YubiKey or Google TitanThat is, ultra-secure storage devices that never expose the private key and only respond to cryptographic challenges. This is where projects like PicoFido fit in perfectly: they allow you to have an inexpensive physical medium to store and use your passkeys.
Using this type of key, you can register passkeys with compatible services and, from there, Log in simply by connecting the key and confirming the actionwithout worrying about leaked passwords, SMS messages that don't arrive, or emails that get lost in the spam folder.
Using Flipper Zero as a U2F key: convenient but with limitations
Another device that has become quite popular among security and ethical hacking enthusiasts is Zero pinball machineIn addition to its usual functions, it includes support for acting as a U2F key, allowing it to be used as a physical authentication factor in a multitude of web services.
With U2F enabled, your Flipper Zero can register as Hardware security key for accounts on Gmail, Dropbox, Slack, Instagram and many other sites that accept the standard. The registration process is relatively quick and only needs to be done once per account.
To configure it, you must first connect the Flipper Zero to the computer via USB cable Then, on the device itself, enter the main menu and select the U2F option. There you will activate the operating mode as a security key.
Then, in your computer's browser, open the account security settings You want to protect something (for example, Google or another service's security settings) and look for the section where you add security devices or physical keys. You start the process of adding a new key and follow the on-screen instructions.
During registration, the service will ask you to confirm the transaction directly from within Flipper. At that point, You press the OK button on the device to authorize it as your U2F key.Once completed, the next time you log in you will be asked to connect the Flipper and confirm with OK to validate access.
It is important to note that, although this feature is very practical and fun, the creators of the device make it clear that Flipper Zero is not intended as a maximum security platformThe recommendation is to use it only for low-risk accounts and avoid it for critical services such as online banking, cryptocurrencies, government procedures, or anything particularly sensitive.
How to use a U2F key with your Google account
One of the most widespread uses of U2F keys is protect Google accountsThese are often the gateway to email, photos, documents, mobile backups, etc. Integrating a physical key here is an excellent idea to increase security.
The first thing is to get one USB key compatible with U2F or FIDO2Whether it's an affordable model (which can be found cheaply in online stores) or a key from well-known brands like Yubico or Google, it's important to check the specifications to ensure it's compatible with these standards.
Next, connect the dongle to your computer and log into your Google account to access the section of Security within your accountThere you will see the Two-Step Verification (2FA) section; if you don't already have it activated, you will have to configure it by following the initial steps with SMS, an authenticator app, or another method.
Once 2FA is activated, you can scroll down the page to the section where physical security keys are addedGoogle will guide you step by step: it will ask you to connect the key, choose the type (USB, NFC, etc.) and touch the button or metal contact on the key to confirm that you are present.
Once you complete the registration, the account will be set up for ask you for the USB key at certain logins or when it detects suspicious activityThus, even if an attacker guesses or steals your password, they will not be able to enter without physically having your key.
In addition to Chrome, other modern browsers such as Firefox, Microsoft Edge, and even Safari They have also been incorporating support for U2F and FIDO2. On macOS, a relatively recent version of the system and browser may be required, but in general, compatibility is quite broad today on Windows, macOS, and Linux, provided the browser supports the standard.
How USB key cryptography works
The security of these keys is not based on software tricks, but on public key cryptography integrated into the device itselfEach key internally generates a key pair: a private key, which never leaves the device, and a public key, which is sent to the service server when you register the key.
When you log in to a protected website, the server sends your browser a random cryptographic challengeThe browser passes it to the physical key, which uses its private key to sign that challenge and returns the signed response to the browser.
The server, which already has the public key associated with your account from the moment of registration, Check the signature of the responseIf it's correct, the system knows that the person responding is your key and validates the authentication. If someone tries to act as an intermediary without having the physical key, they won't be able to generate a valid signature.
An interesting aspect is that the The key never reveals the private key or personally identifiable informationNeither the server nor an attacker intercepting the traffic can extract your secret; they only see signed challenges and responses. This greatly reduces your digital footprint and attack surface.
In addition, many models implement mechanisms for prevent them from being used as cross-site trackersThis generates unique identifiers for each service instead of a global ID. This way, even if the same key is used on multiple websites, they cannot easily cross-reference the information to profile the user.
Advantages and disadvantages compared to other 2FA methods
If we compare U2F and FIDO2 keys with other two-step authentication methods, their differences are clearly visible. strengths and weaknessesIdeally, you should familiarize yourself with them to decide which one best suits your daily needs.
Authentication apps, such as Google Authenticator or Authy, generate Temporary codes from your own mobile phoneThey have the advantage of not requiring extra hardware and work even without an internet connection, but they are still vulnerable to phishing attacks where you are tricked into entering the code on a fake website.
SMS and phone calls are probably the simplest and most widespread method: You receive a verification code that you must copy to complete access. The problem is that they depend on the mobile network, can fail or arrive late, and there are also SIM swap attacks and other frauds that have shown that this system is not as robust as thought.
The push notifications sent by some official apps are quite convenient: You just have to approve or reject the request on your mobile phone.However, you still depend on your phone, and in certain attacks, they may try to overwhelm you with requests so that you accept one by mistake.
USB drives, on the other hand, offer a far superior protection against phishingBecause there's no code that the user can be tricked into entering elsewhere. Furthermore, they don't depend on mobile coverage and typically work across multiple platforms. The main disadvantage is that they require carrying a physical device and assuming the risk of loss or damage.
That's why it's always recommended to configure at least two security keys and combine this system with other recovery methods, such as backup emails or phones, so you don't get locked out permanently if the main key disappears.
What happens if you lose your USB key: recovery and best practices
A logical concern when you start using these types of devices is What happens if you lose the key or it stops working?Nobody wants to protect their account so much that they can't even log back in themselves.
Large services, such as Google and other providers, offer multiple recovery optionsTypically, you can add a recovery phone number, an alternate email address, and backup codes for emergencies. It's a good idea to take a few minutes to set all of this up from the start.
The most important thing is to register more than one physical security key in your account. This way, if you lose the one on your keychain, you can use another one you have stored at home or in a safe place to continue accessing your account and, if necessary, revoke the lost one.
If none of the keys are available, there is always the account recovery process that each service makes available to you, where they will ask you a series of questions, send codes to alternative means and, sometimes, manually review your case.
If you reach that point and can't regain access using the automated forms, the next step is contact the service's technical supportIt's not always quick or easy, but in certain situations they can help you verify your identity through other means.
With all this in mind, the best strategy is a combination: two registered physical keys, well-configured recovery methods, and some order to know where everything is. This way you can benefit from the superior security of U2F keys without fear of being locked out of your own account.
Ultimately, U2F and FIDO2-based USB security keys have become an incredibly powerful tool for protecting your accounts against increasingly sophisticated attacks. Whether you buy a commercial key, repurpose a USB drive with programs like USB Raptor to protect your PC, create your own key with a Raspberry Pi Pico, or experiment with Flipper Zero for less critical accounts, having a physical security measure that can't be stolen remotely makes a huge difference to your online security.
Passionate writer about the world of bytes and technology in general. I love sharing my knowledge through writing, and that's what I'll do on this blog, show you all the most interesting things about gadgets, software, hardware, tech trends, and more. My goal is to help you navigate the digital world in a simple and entertaining way.